Search
Ethical Hacking and Cyber Security MSci/BSc (Hons)
Study level: Undergraduate
Dive into cyber security, ethical hacking, digital forensics and secure networking. Learn practical skills, gain knowledge and build towards a future-proof cybersecurity career.
Course features
Course option
Year of entry
Location
Coventry University (Coventry)
Study mode
Full-time
Sandwich
Duration
BSc:3 years full-time4 years sandwich
MSci:4 years full-time5 years sandwich
UCAS codes
GG45 / I120
Start date
September 2026
November 2026
January 2027
March 2027
May 2027
July 2027
Course overview
This course could be the right fit for aspiring cybersecurity professionals, tech enthusiasts and problem-solvers who want practical skills in ethical hacking, network security and digital forensics. Gain industry-relevant expertise through labs, and real-world projects to launch your career. With this course, you could benefit from opportunities for hands-on learning, industry placements and an integrated master's degree (subject to meeting progression standards).2
Key course highlights
- Practical ethical hacking: learn penetration testing, web security and exploit development in dedicated hacking labs.
- Security and forensics: master risk management, secure network infrastructures, incident response and digital evidence analysis.
- Industry-aligned learning: apply skills through 'Capture the Flag’ challenges, simulations and collaborative projects.
Rated Gold Overall
Teaching Excellence Framework (TEF) 20235 QS Stars for Teaching and Facilities
QS Stars University RatingsTop 5 Student City in England (Coventry)
QS Best Student Cities Index 2026Why you should study this course
- Hands-on, industry-relevant skills: gain real-world expertise through practical labs, penetration testing exercises and ‘Capture the Flag’-style challenges in dedicated hacking labs.
- Career-focused learning: master in-demand areas like ethical hacking, network security and digital forensics—directly aligned with industry roles such as penetration tester, security operation centre analyst or forensic investigator.
- Active industry engagement: employability is at the core of our courses, and as such we aim to provide you with optional industry guest lectures and networking events to help you stand out from the crowd (subject to availability).2
- Modern facilities: train in specialist on-campus ethical hacking and computing labs with professional tools, simulating real cyber threats in a controlled environment.4
- Enjoy a seamless progression route: with an integrated master's year, you get the opportunity to study a master’s degree while paying undergraduate fees (subject to meeting progression standards).
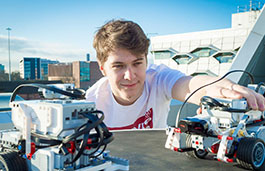
Why I chose Ethical Hacking and Cyber Security
Stefan shares his journey studying Ethical Hacking and Cyber Security at Coventry University, from hands-on lab experiences to building the skills that will shape his future career.
Read more
What you'll study
This course is designed to equip you with practical and theoretical expertise in cybersecurity. Learn about programming, ethical hacking techniques, risk management and incident response, and prepare for roles such as penetration tester, security analyst or forensic investigator. With industry-aligned modules and specialist labs, you should feel confident to tackle evolving cyber threats and security challenges after you graduate. Please note that further study opportunities are subject to competitive application, availability, meeting any applicable visa requirements and additional costs may apply.
We regularly review our course content, to make it relevant and current for the benefit of our students. For these reasons, course modules may be updated.
How you'll learn
Your course will be based on a series of lectures, with associated seminars and project-based practical classes.
In addition, your personal tutor will review and discuss your progress with you and provide advice. You will be expected to engage in both class and online activities and discussions. Each module will also require you to participate in additional guided reading and self-directed study, to reinforce the learning gained from timetabled sessions.
We believe that the best way of learning is through doing - applying the theoretical concepts to practical problems. Throughout the course, emphasis is placed on the practical development of work, with a significant portion of your time being spent on assisted lab tasks, which may involve live practical hacking challenges, seminars discussing topics such as cryptography and secrecy or project-based classes, which may involve more in-depth work developing secure systems in hostile environments2.
Teaching contact hours
As a full-time undergraduate student, you will study modules totalling 120 credits each academic year. You will normally study one 30-credit module at a time. A typical 30-credit module requires a total of 300 hours of study made up of teaching contact hours, guided and independent study.
Teaching hours
Teaching hours may vary depending on your year of study and selected modules. During your first year, you can expect 12-15 teaching hours each week. You will also have the option to attend additional sessions, including time with a progress coach or to meet with staff for advice and feedback. As you progress through your studies, teaching hours may reduce.
Guided and independent study
Throughout your studies, you will be expected to spend time in guided and independent study to make up the required study hours per module. You'll be digging deeper into topics, review what you've learned and complete assignments. This can be completed around your personal commitments. As you progress through your studies, you'll spend more time in independent study.
Online learning
As an innovative university, we use different teaching methods including online tools and emerging technologies. So, some of your teaching hours and assessments may be delivered online
Assessment
This course will be assessed using a variety of methods which could vary depending upon the module.
Assessment methods may include:
- formal examinations
- phase tests
- essays
- group work
- presentations
- reports
- projects
- coursework
- exams
- individual assignments
- laboratories.
The Coventry University Group assessment strategy ensures that our courses are fairly assessed and allows us to monitor student progression towards achieving the intended learning outcomes.
Entry requirements
Typical entry requirements:
Not got the required grades? We offer this degree with an integrated foundation year.
Fees and funding
| Student | Full-time | Part-time |
|---|---|---|
| UK, Ireland*, Channel Islands or Isle of Man | £9,790 per year | Not available |
| EU | £9,790 per year with EU Support Bursary** £20,800 per year without EU Support Bursary** |
Not available |
| International | £20,800 per year | Not available |
If you choose to study this course with a professional placement2 or study abroad year, you will need to pay a tuition fee3 to cover your academic support throughout your placement year. Students commencing their professional placement in the academic year 2028/29 will pay £1,575 if they are paying UK fees, or £1,900 if they are paying international fees.
For advice and guidance on tuition fees and student loans visit our Undergraduate Finance page and see The University’s Tuition Fee and Refund Terms and Conditions.
The University will charge the tuition fees that are stated in the above table for the first Academic Year of study. The University will review tuition fees each year. For UK (home) students, if Parliament permits an increase in tuition fees, the university may increase fees for each subsequent year of study in line with any such changes. Note that any increase is expected to be in line with inflation.
If you choose to study this course with a professional placement, the University will charge the tuition fees stated above for those on a placement during Academic Year 2028/29. The University will review professional placement tuition fees each year. For UK (home) students, the University may increase fees for each subsequent year of study, but such that it will be no more than 5% above inflation.
For international students, we may increase fees each year, but such increases will be no more than 5% above inflation. If you defer your course start date or have to extend your studies beyond the normal duration of the course (e.g. to repeat a year or resit examinations) the University reserves the right to charge you fees at a higher rate and/or in accordance with any legislative changes during the additional period of study.
We offer a range of International scholarships to students all over the world. For more information, visit our International Scholarships page.
Tuition fees cover the cost of your teaching, assessments, facilities and support services. There may be additional costs not covered by this fee such as accommodation and living costs, recommended reading books, stationery, printing and re-assessments should you need them. Find out what's included in your tuition costs.
The following are additional costs not included in the tuition fees:
- Any optional overseas field trips or visits: £400+ per trip.
- Any costs associated with securing, attending or completing a placement (whether in the UK or abroad).
*Irish student fees
The rights of Irish residents to study in the UK are preserved under the Common Travel Area arrangement. If you are an Irish student and meet the residency criteria, you can study in England, pay the same level of tuition fees as English students and utilise the Tuition Fee Loan.
**EU Support Bursary
Following the UK's exit from the European Union, we are offering financial support to all eligible EU students who wish to study an undergraduate or a postgraduate degree with us full-time. This bursary will be used to offset the cost of your tuition fees to bring them in line with that of UK students. Students studying a degree with a foundation year with us are not eligible for the bursary.
Facilities
Your studies will be centred in high-specification learning environments that benefit from extensive social learning facilities, well-appointed laboratories, lecturing facilities and classrooms, facilitating our innovative teaching methods across a diverse suite of courses.
- Ethical Hacking Lab: a course-specific room with custom operating systems and software, which allows you to reconfigure the set-up in order to practice your hacking techniques.
- Networking Lab: which allows you to build and test the physical network.
Facilities are subject to availability4. Access to some facilities (including some teaching and learning spaces) may vary from those advertised and/or may have reduced availability or restrictions where the university is following public authority guidance, decisions or orders.
Careers and opportunities
Upon successful completion of the course, you should be able to:
- understand, categorise and discuss threats to computer systems and services
- apply sound investigations and reporting procedures to identify and report issues in systems, or as part of a forensic investigation
- apply research and problem-solving skills to a security-related project.
We encourage our graduates to come back to give guest talks, meet (and often recruit) the current students and take part in extracurricular events (subject to availability)2.
Where our graduates work
Past graduates of Coventry University have found work in penetration testing, digital forensics and network security. Working for organisations such LRQA Nettitude Cyber Security Services, Janet, the BBC and the UK government. Other students have gone on to successful careers outside of security, in software development roles.
The graduate destinations listed above illustrate potential career paths. You may need to gain additional qualifications or practical experience, pass professional examinations, complete training, cover associated costs and meet specific visa or immigration requirements to secure employment in these fields.

Discover Phoenix+
Phoenix+ brings you together with other students to learn, experience and develop essential knowledge and skills. Whatever destination you choose, it's about preparing you for life after university.
Learn more about Phoenix+How to apply
You may also like
Computer Science MSci/BSc (Hons)

Data Science MSci/BSc (Hons)