PhD student wins Postgraduate of the Year Award 2025
Angelika Berg, a PhD student investigating gender-based harassment on public transport, has been named Coventry University’s Postgraduate Researcher (PGR) of the Year 2025.
Search
Our research in future transport and cities is at the forefront of mobility innovation in a rapidly changing technology-enabled world.
We see major disruption in the transport sector due to the imminent arrival of future technology such as connected and automated mobility. As a result of this, the way in which people, goods and services move is changing dramatically and we are guiding that change.
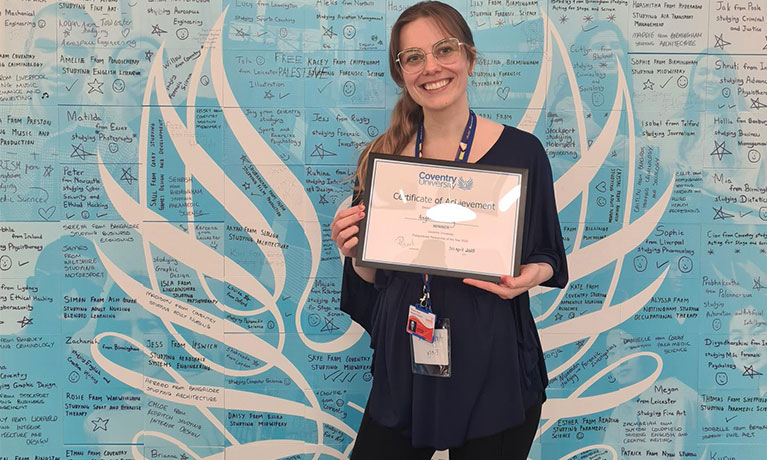
Angelika Berg, a PhD student investigating gender-based harassment on public transport, has been named Coventry University’s Postgraduate Researcher (PGR) of the Year 2025.

Emily Nash, a PhD researcher exploring how to make rail travel more accessible for people with sight loss, has won Coventry University’s ‘Three Minute Thesis’ (3MT®) competition 2025.
The National Centre for Accessible Transport (ncat) aims to make transport accessible for all by providing people-centred evidence, insights and solutions that inform policy, influence investment and address barriers faced by disabled people across the UK.
Find out more